You’ll learn about:
- Effective data handling processes that keep information safe.
- Explore the role of encryption and hashing in safeguarding information.
- Explore the role of encryption and hashing in safeguarding information.
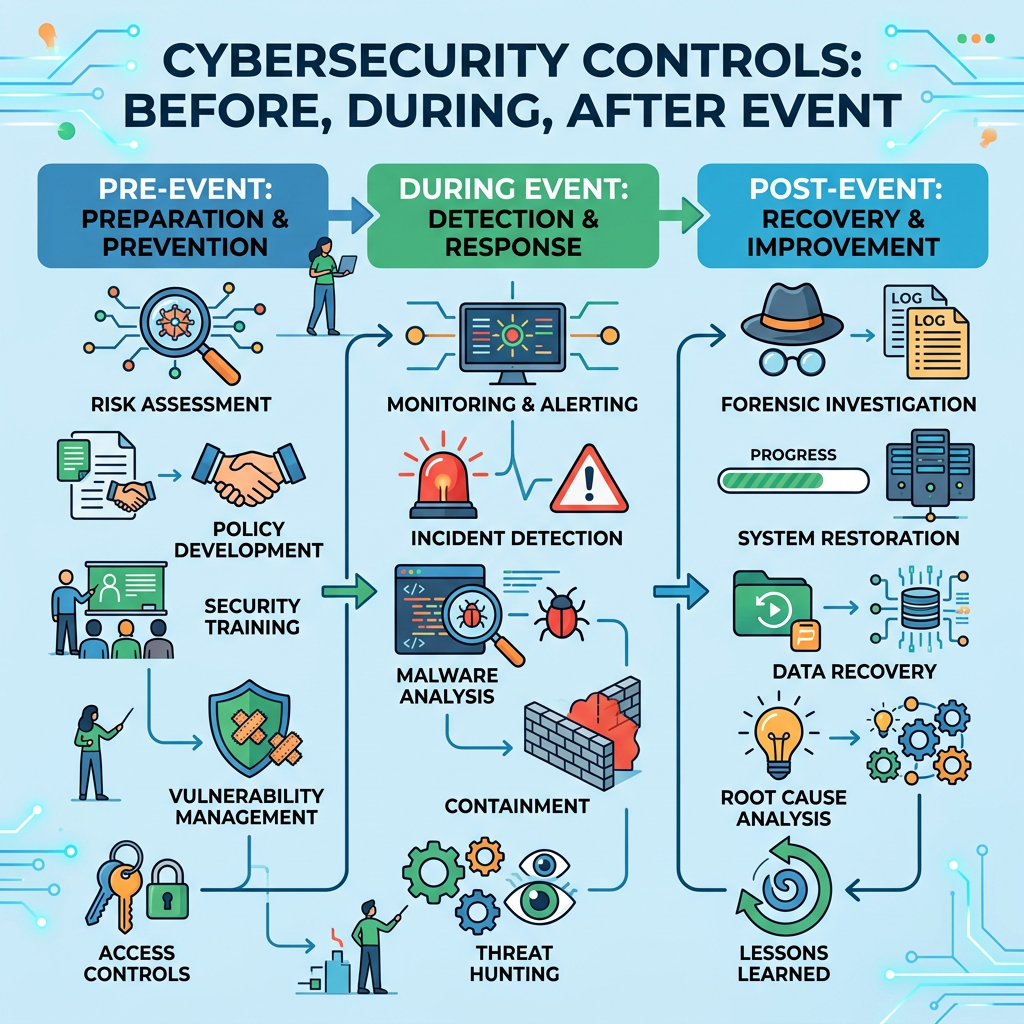
- Standard access controls that companies use to authorize and authenticate users.
Alright, are you ready to keep moving ahead
Course Instructor
Free
FREE
Protect Organizational Assets
Welcome to Module 2
Principle of least privilege
The data lifecycle
Activity: Quiz
Leave a Reply